
Ağ Güvenliği 101 #4: Bilgi Toplama #1: Ping, Whois Nasıl Çalışır?,CyberOps, RIPE | by Eşref Erol | Three Arrows Security | Medium
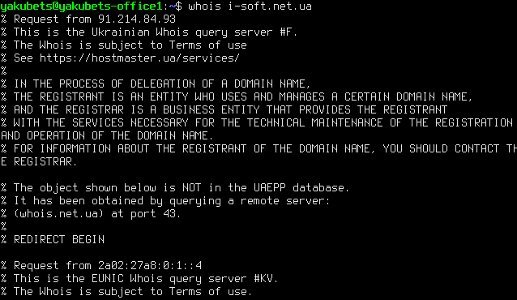
skull-hacker-complete-tcp-ip-app-ping-finger-anonimys-e-mailer-whois-irc-firewall-tool-and__1-39807/IP.txt.txt at master · Planet-Source-Code/skull-hacker-complete-tcp-ip-app-ping -finger-anonimys-e-mailer-whois-irc-firewall-tool-and__1-39807 · GitHub









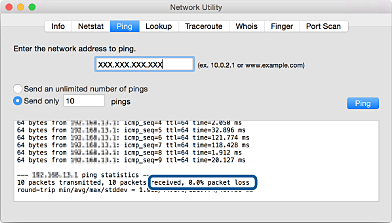





:max_bytes(150000):strip_icc()/icmp-ping-5e5d3a24ff584d289d918cbb7c306d51.png)
